301![Umesh Shankar http://www.umeshshankar.com [removed] Education University of California, Berkeley[removed]) Umesh Shankar http://www.umeshshankar.com [removed] Education University of California, Berkeley[removed])](https://www.pdfsearch.io/img/1a4ae103a618062f996f0aa96934c0bc.jpg) | Add to Reading ListSource URL: umeshshankar.comLanguage: English - Date: 2011-12-20 17:32:51
|
|---|
302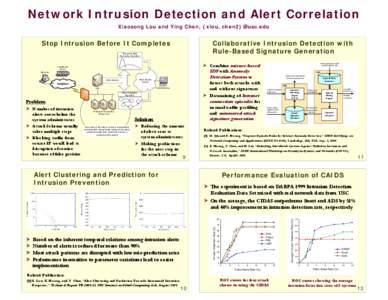 | Add to Reading ListSource URL: gridsec.usc.eduLanguage: English - Date: 2005-08-30 20:28:11
|
|---|
303![SHUBHANSHU MISHRA PhD Student, Graduate School of Library and Information Science [removed] | linkedin.com/in/shubhanshumishra | github.com/napsternxg | +[removed]Academic Achievements Education SHUBHANSHU MISHRA PhD Student, Graduate School of Library and Information Science [removed] | linkedin.com/in/shubhanshumishra | github.com/napsternxg | +[removed]Academic Achievements Education](https://www.pdfsearch.io/img/c4575a6a365a55afb077e5c2f28ce66f.jpg) | Add to Reading ListSource URL: shubhanshu.comLanguage: English - Date: 2014-06-29 04:03:31
|
|---|
304 | Add to Reading ListSource URL: www.netmode.ntua.grLanguage: English - Date: 2004-05-28 14:14:29
|
|---|
305 | Add to Reading ListSource URL: filesystems.orgLanguage: English - Date: 2012-09-07 11:07:02
|
|---|
306 | Add to Reading ListSource URL: inac.free.frLanguage: English - Date: 2005-08-03 14:14:48
|
|---|
307 | Add to Reading ListSource URL: www.icir.orgLanguage: English - Date: 2007-01-16 15:06:05
|
|---|
308 | Add to Reading ListSource URL: www.icir.orgLanguage: English - Date: 2007-01-16 15:06:05
|
|---|
309 | Add to Reading ListSource URL: ids.cs.columbia.eduLanguage: English - Date: 2011-09-04 10:44:35
|
|---|
310 | Add to Reading ListSource URL: h20195.www2.hp.comLanguage: English |
|---|